What anti-tampering and anti-counterfeiting technical features do Java chip cards possess?
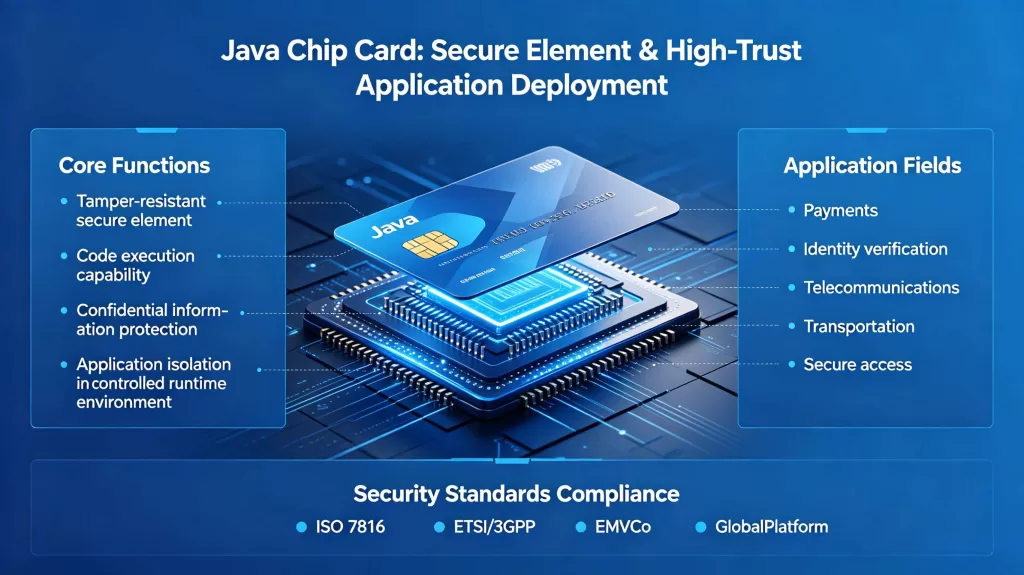
Java chip cards are not merely smart cards; they are tamper-resistant secure elements capable of executing code, protecting confidential information, and isolating different applications within a strictly controlled runtime environment. In fields such as payments, identity verification, telecommunications, transportation, and secure access, they must resist physical probing, protect sensitive data, verify their own authenticity, and reject unauthorized software or incorrect updates. At the same time, they comply with security element standards such as ISO 7816, ETSI/3GPP, EMVCo, and GlobalPlatform, enabling their deployment in high-trust applications.
From a product and security perspective, the Java card platform isolates applets, uses firewalls to protect internal objects, supports secure messaging, and provides dedicated encryption APIs. These features lay the technical foundation for tamper- and counterfeit-proofing in application scenarios such as payments, identity verification, telecommunications, access control, and transportation.
Core Platform Protection Mechanisms Shield Java Chip Cards from Tampering
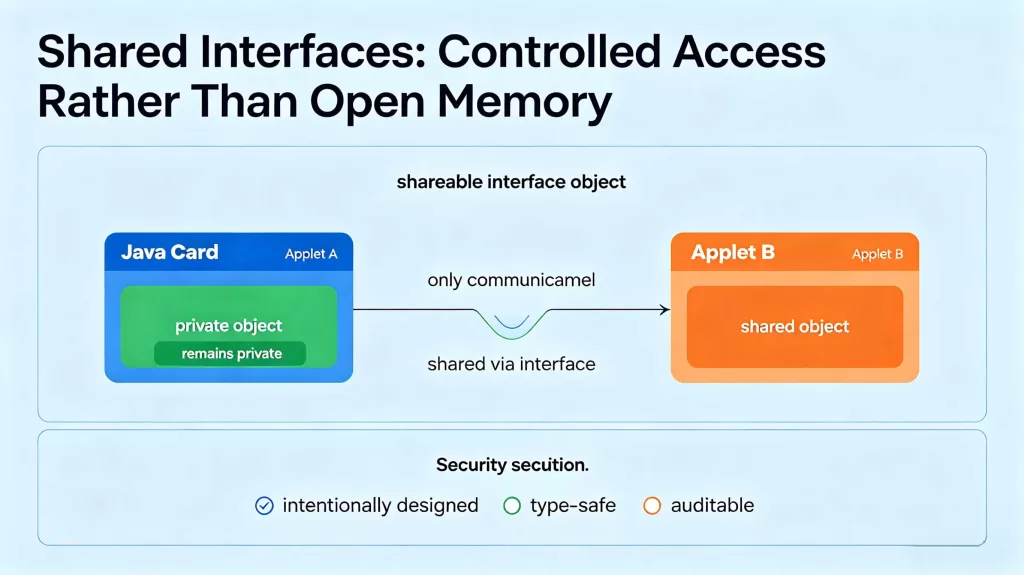
The most powerful anti-tampering feature of Java smart cards begins with runtime isolation. The Java smart card runtime environment requires isolation between contexts and applets, meaning that unless another applet explicitly exposes an access interface, one applet cannot access the fields or objects of another applet.
The Java smart card firewall is enforced at runtime; it prevents unauthorized access to object fields and methods, and even to the length and contents of arrays created by other applets. Equally important, the firewall also protects objects owned by the Java Card runtime environment itself.
Malicious or compromised applets may attempt to read, overwrite, or reuse data belonging to other applications. On a Java Card, this approach will not work unless the owner intentionally shares access through a shared interface object.
Shared Interfaces: Controlled Access Rather Than Open Memory
Java Card allows collaboration between applications, but only in a standardized manner. It uses shareable interface objects as the sole standard means for sharing objects between applets. This design enables developers to achieve interoperability without turning the card into a chaotic shared-memory environment. In other words, Java Card does not compromise isolation to support business logic; it maintains isolation while adding a narrow, explicit access channel on top of it.
The Java Card platform enforces that these interfaces must be intentionally designed, type-safe, and auditable. When card issuers or solution providers review applet designs, they can precisely see which objects are shared and which remain private. This visibility reduces the attack surface and improves the quality of security reviews.
Protecting Commands and Responses in Java Card Transactions
The protection of Java Chip Cards extends beyond the chip boundary. The GlobalPlatform Secure Channel protocol provides authenticated, protected communication between off-card entities and the card. In the current GlobalPlatform card specifications, Secure Channel Protocol 03 uses AES encryption to protect bidirectional communication by decrypting and MAC-verifying incoming commands, then encrypting and generating a MAC for the card’s response. The specification also stipulates that an authenticated out-of-card entity knows the keys required to initiate a secure session. This mechanism serves as a direct anti-tampering control. Without a secure channel, an attacker might attempt to tamper with personalization data, inject malicious commands, or replay previously captured traffic.
Anti-counterfeiting Features to Enhance the Security of Java chip Cards Deployments
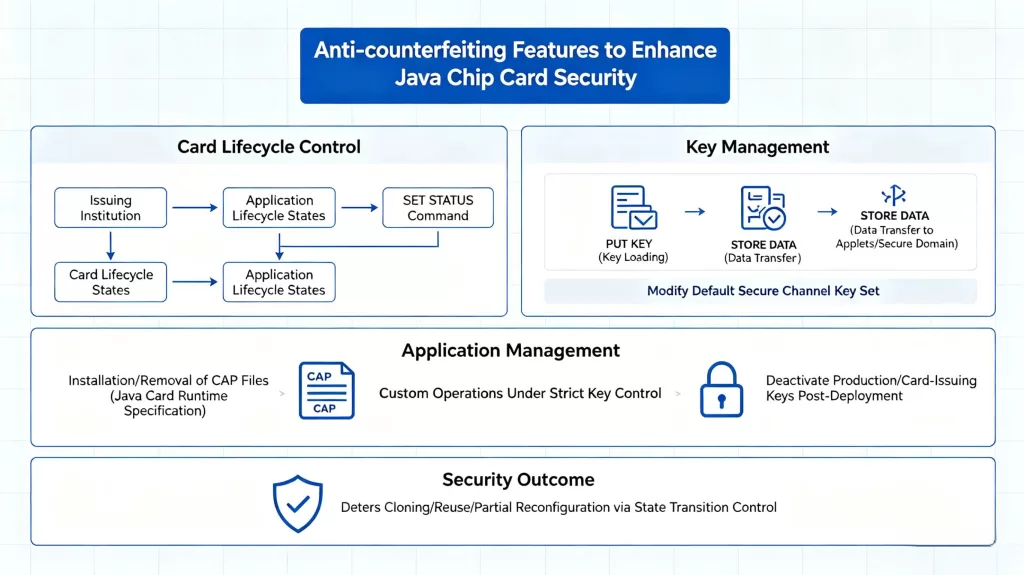
Anti-counterfeiting depends not only on the card’s inherent features but also on the extent to which the issuing institution controls its lifecycle. According to Oracle GlobalPlatform support documentation, the platform supports managing card lifecycle states or application lifecycle states via the SET STATUS command, loading keys via PUT KEY, and transferring data to applets or the issuer’s secure domain via STORE DATA. It even allows modification of the default secure channel key set. The Java Card Runtime Specification also covers application management, including the installation and removal of CAP files.
You must handle any custom operations under strict key control, and you should deactivate production keys or card-issuing keys after deployment. By requiring issuers to control state transitions, Java Card makes it more difficult for malicious actors to clone, reuse, or partially reconfigure cards without detection.
Delivering enhanced security in payment, identity verification, telecommunications, and other sectors
Different industries require different business rules, but they all require trust. The Java Card API’s compatibility encompasses various standards used in secure elements, including ISO 7816 and ETSI/3GPP mobile communication standards, upon which major industry standards such as EMVCo and GlobalPlatform are built. It is this interoperability that enables a single security architecture to serve payment card, SIM, and eSIM, digital identity, transit card, and enterprise access credential ecosystems.
- In the payment sector, anti-counterfeiting security enables cards to self-authenticate and protect transaction data.
- In the authentication sector, it means cards can prove their legitimacy without revealing private keys.
- In the telecommunications sector, Java smart card configuration and remote management can be performed under strict secure channel controls.
- For access control, this means the card remains trustworthy even when it must coexist with other applications on the same chip.
In all cases, the same technical pattern repeats: isolating applets, verifying management channels, protecting keys, and controlling the lifecycle. This is the core security formula of the Java smart card.
Delivering Security in a Threat-Ridden Environment
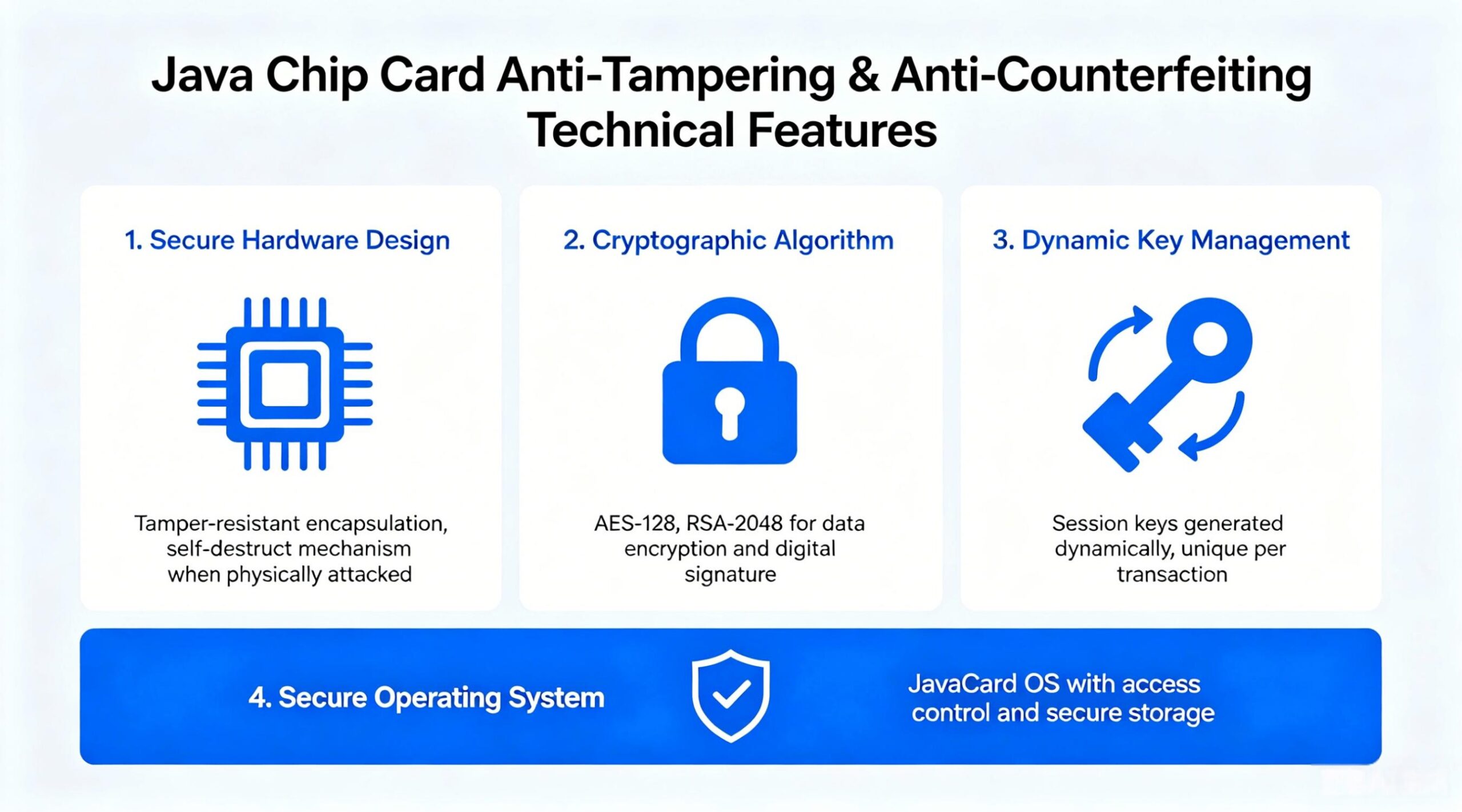
The Java chip card effectively prevents tampering and counterfeiting by integrating four layers of security protection onto a single platform. First, the Java card firewall isolates applets, blocking unauthorized access to data and methods. Second, the GlobalPlatform secure channel protects commands and responses, preventing arbitrary tampering or replay of administrative traffic. Third, the Java Card cryptographic API provides support for signing, random number generation, key management, and encryption, enabling the card to authenticate itself cryptographically. Fourth, lifecycle control and personalization commands ensure that card issuers can control the card’s functionality, execution time, and the keys used.
This is precisely what makes the Java chip card a solid foundation for secure applications.


