The 125 kHz RFID card remains one of the most widely used low-frequency cards today, offering organizations a fast, stable, and easily deployable method for the proximity identification of individuals or objects. Furthermore, it boasts rapid read speeds, performs exceptionally well in controlled-access environments, and can be deployed at scale without a complex technical ecosystem. […]
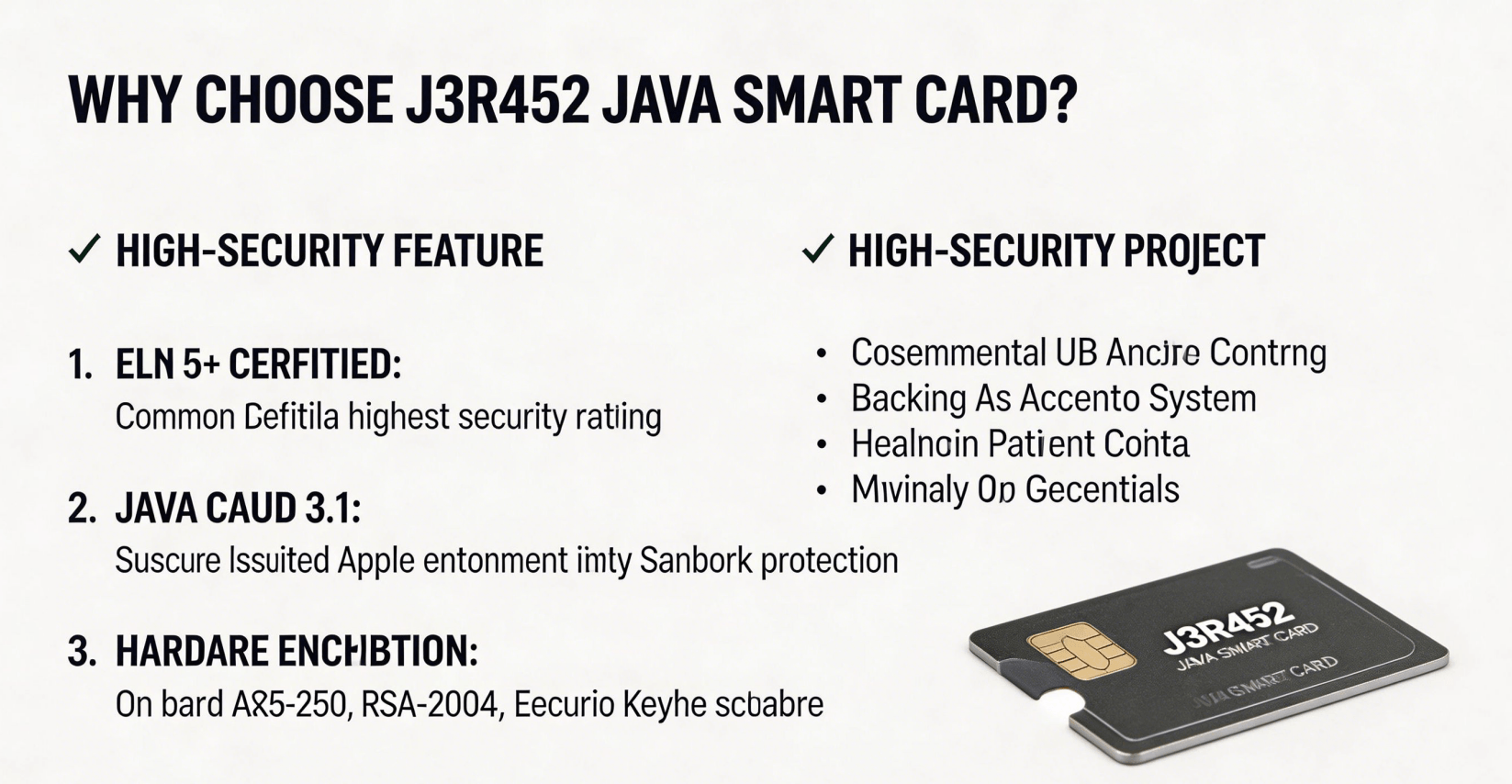
High-security projects choose Java smart cards because they can withstand technical reviews, operational stress, and the demands of a long lifecycle. The NXP P71 JCOP 4.5 J3R452 Java smart card is a dual-interface JCOP 4.5 card based on the P71D600/SmartMX3 platform, running Java Card 3.0.5 Classic and GlobalPlatform 2.3.1. This combination meets the operational requirements […]
In the global financial payments industry, the security level of a smart card chip directly determines whether it can be used for credit card transactions, cross-border payments, and high-security authentication. Modern payment systems no longer evaluate chips solely by storage capacity or communication speed; instead, they focus on whether the chip has passed internationally recognized […]
When using a smart card platform for financial payments, users do not prioritize brand or memory capacity. Instead, they focus on whether the chip can ensure secure, fast, and predictable transactions every time a cardholder taps, inserts, or reuses the card. In the payment sector, reliability is at the core of smart cards. That is […]
The operating frequency of an RFID smart card determines its communication method, read range, security, and optimal use cases.Selecting the appropriate frequency requires balancing technical performance with actual business needs.125 kHz RFID cards may be ideal for simple access control.13.56 MHz RFID cards, on the other hand, may be better suited for secure identity verification, […]
Java chip cards are not merely smart cards; they are tamper-resistant secure elements capable of executing code, protecting confidential information, and isolating different applications within a strictly controlled runtime environment. In fields such as payments, identity verification, telecommunications, transportation, and secure access, they must resist physical probing, protect sensitive data, verify their own authenticity, and […]
When using public transportation, transit cards must be secure, reliable, and fast enough. If the card is too slow, passengers will complain, wait times will increase, and on-time performance will be compromised. Some of our Java cards are specifically designed for secure, multi-application transit cards, supporting both contact and contactless payments, fast transaction speeds, secure […]
Slow transaction processing speeds for payment cards can ripple through every stage of the process. Users will first notice the delay, and merchants will subsequently experience longer wait times, reduced terminal throughput, increased workflow interruptions, and a diminished overall experience. Consequently, speed has become a core criterion for users selecting Java cards. The J3R150 Java […]
A Java SIM card is a smart SIM card embedded with the Java Card platform. Beyond providing the identity authentication and storage capabilities of traditional SIM cards, it can also execute customized Java applications such as carrier services, security authentication, NFC payments, and more. The 64KB and 128KB figures refer to the available storage capacity. […]
When deployed in a financial environment, a payment card is far from being just an ordinary piece of plastic; it serves as a secure computing environment, a secure transaction interface, and the very foundation of trust for the entire payment experience. The Samsung S3FT9MG Java Smart Card works especially well for financial payment applications because […]